
In our last blog, we spoke about fighting spam emails and creating filters. These filters help sift through malicious and legitimate emails. In this blog, we’ll look at one of the latest scams to surface the internet; CEO Email Spoofing
We’ve been hearing of a popular scam that’s doing the rounds at the moment. This particular one uses email spoofing in order to manipulate employees. Employees are then convinced to make bank payments to false accounts.
A. “Email spoofing is the forgery of an email header so that the message appears to have originated from someone or somewhere other than the actual source”.
What’s the ‘CEO Email Spoofing’ scam then?
Scammers are now targeting businesses, pretending to be CEO’s and emailing employees in finance departments. They will often make out that they are rushed for time. They’ll then ask members of staff to transfer sums of money to false bank accounts.
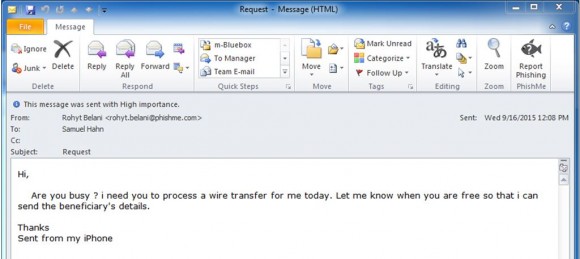
It looks very real, doesn’t it? Even the fact that the standard iPhone signature was used, somehow seems more personal and real. We spoke to Gary Ennis, owner of NSDesign Ltd, who’s company was targetted:
It was a normal day in the office – the whole team were in and the day was going as planned. One of my colleagues who deals with our finances recieved an email, which looked genuine, from ‘me’. She then raised the question about how much was to be transferred (as per this email) and it was then that we discovered how close we were to being caught out.
-Gary Ennis, NSDesign Ltd.
The scary thing about this scam is that it often slips through spam prevention. The reason for this? These are single-sent emails, aimed specifically at one particular business. This is different from the usual mass email spam.
What to look out for…
Check both the ‘from’ and ‘reply-to’ email address. These addresses may look similar to your companies domain name – when in fact, one letter is missing or has been replaced. This is very common for companies including the letter ‘L’ for example – this is often replaced with a ‘1’ or ‘I’. The CEO Email Spoofing scam can also contain a random ‘reply-to’ address – which, when seen, should flash warning lights in your head! We’d advise you to delete that email ASAP!
Additionally, you should ensure that the domain extension is correct – for example using ‘.uk’ instead of ‘.co.uk’ or ‘.co’ instead of ‘.com’.
Moving forward…
Businesses are urged to use two-factor authentication wherever possible – and that includes banking and social media. It also won’t hurt to physically speak to that colleague. If you’re in a small business, you may be lucky enough to be able to physically walk over to your colleague to ask. Failing that, why not give them a call or message them on your internal chat?
Hopefully, these tips have helped you! Why not share them on social media for others to benefit from? Have a question? Feel free to comment below, or tweet us!
Leave a Reply
